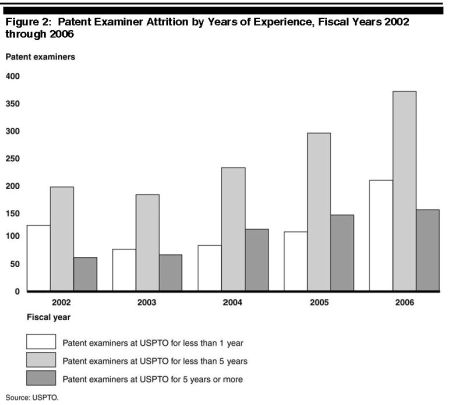
Wednesday the Government Accountability Office released a report [Summary] [Full Report] that found “it is unlikely that the [Patent Office] will be able to reduce the growing backlog simply through its hiring efforts.” The report provided, “The agency has also estimated that if it were able to hire 2,000 patent examiners per year in fiscal year 2007 and each of the next 5 years, the backlog would continue to increase by about 260,000 applications, to 953,643 at the end of fiscal year 2011.” Therefore the report stated, “Despite its recent increases in hiring, the agency has acknowledged that it cannot hire its way out of the backlog and is now focused on slowing the growth of the backlog instead of reducing it.”
Software and Information Industry Association Questions State Immunity
 The Software and Information Industry Association (SIIA) filed an amici curiae brief asking U.S. Supreme Court to hear a case where State sovereign immunity for patent infringement is at issue. The issue is whether a State waives its Eleventh Amendment immunity in patent infringement actions by regularly and voluntarily nvoking federal jurisdiction to enforce its own patent rights. The SIIA asserts that it is equitable for States to have immunity from damages for patent infringement while they are free to sue private sector organizations for violations of State held intellectual property rights. The SIIA joined the U.S. Camber of Commerce in filing the brief.
The Software and Information Industry Association (SIIA) filed an amici curiae brief asking U.S. Supreme Court to hear a case where State sovereign immunity for patent infringement is at issue. The issue is whether a State waives its Eleventh Amendment immunity in patent infringement actions by regularly and voluntarily nvoking federal jurisdiction to enforce its own patent rights. The SIIA asserts that it is equitable for States to have immunity from damages for patent infringement while they are free to sue private sector organizations for violations of State held intellectual property rights. The SIIA joined the U.S. Camber of Commerce in filing the brief.
BMPG v. Calf Dept of Health Services, No. 07-956 [Docket Link] [SIIA Brief] [SIIA Press Release].
Intellectual Property Resources
European Patent Attorney Ralph Beier has compiled a massive list of links to intellectual property related websites worldwide. [link]
As of today he lists:
- Intellectual Property Offices (110)
- Intellectual Property Organizations (103)
- IP Database Providers (22)
- Official Registers and Databases (114)
- Official Examination Guidelines and Publications (14)
- IP Classifications Standards (4)
- Official Gazettes (24)
- Courts (58)
- Texts of Legal Regulations (13)
- Case Law Databases (11)
Ralph’s list is a great resource worthy of a place in any intellectual property attorney’s bookmark list.
IAM on In re Bilski: Tightening The Standards For Software Patents
 Joff Wild of IAM Magazine predicts that the Federal Circuit’s en banc rehearing of the In re Bilsk case signals a move to restrict the patentability of software and business methods. He predicts that the Federal Circuits decision will bring the United States closer in line with how Europe treats this subject matter.
Joff Wild of IAM Magazine predicts that the Federal Circuit’s en banc rehearing of the In re Bilsk case signals a move to restrict the patentability of software and business methods. He predicts that the Federal Circuits decision will bring the United States closer in line with how Europe treats this subject matter.
He provides the following reasons:
- Its rare for cases to be heard en banc
- The Federal Circuit is aware that recently the U.S. Supreme Court has been placing limits on patent holders rights
- Congress is considering the Patent Reform Act and the Federal Circuit’s Chief Judge is opposed to the changes in the Patent Reform Act
Rule 35 [link, PDF] of the Federal Circuit Rules of Practice provides that an en banc rehearing is ordered by a majority vote of the active circuit judges. It states that en banc rehearing is not favored and ordinarily will not be ordered unless:
- en banc consideration is necessary to secure or maintain uniformity of the court’s decisions; or
- the proceeding involves a question of exceptional importance.
Here, the court may be answering the Board of Patent Appeals and Interference’s (Board) request for guidance in determining what is patentable subject matter under section 101. The Board stated in its decision [PDF] that “Several major analyses of statutory subject matter [under section 101] have been published recently.” The Board continued, “The USPTO is struggling to identify some way to objectively analyze the statutory subject matter issue instead of just saying ‘We know it when we see it.’ ”
It is possible that the Federal Circuit could provide a framework for determining patentable subject matter under section 101 without restricting the patentability of software and business methods. However, it may also be that the Federal Circuit will provide a section 101 framework that restricts software and business method patents.
Method of Rewarding Waiting Customers
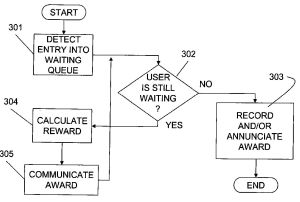 A statement in a IBM patent application caught my eye and made me wonder whether the yet-to-be-released-results of the Federal Circuit’s en Banc rehearing of In re Bilski [Patently-O’s coverage] could effect the patentability of the claims in this application. In Bilski the court will consider, among other things, whether a method or process must result in a physical transformation of an article or be tied to a machine to be patent-eligible subject matter under section 101.
A statement in a IBM patent application caught my eye and made me wonder whether the yet-to-be-released-results of the Federal Circuit’s en Banc rehearing of In re Bilski [Patently-O’s coverage] could effect the patentability of the claims in this application. In Bilski the court will consider, among other things, whether a method or process must result in a physical transformation of an article or be tied to a machine to be patent-eligible subject matter under section 101.
The IBM patent application involves a method of reducing waiting-customer dissatisfaction by monitoring a waiting queue, calculating rewards based on the wait, and communicating the reward to the customer. A customer may be waiting on the phone, or at recreational, restaurant or lodging facilities. The IBM application provides, “although the concepts of the present invention are exemplarily discussed above as having been implemented as an automated system on a computer . . . [the] concepts of the present invention could be implemented completely devoid of computerization or automation of any kind.”
However, it is important to focus on what the application claims. Here, claim 1 provides:
A system for reducing customer dissatisfaction for waiting, said system comprising:a queue monitoring subsystem that detects an entry of a customer into a waiting queue;a reward computing subsystem that calculates a reward for the customer for being in the waiting queue; and a communication subsystem to communicate the reward to the customer, wherein at least one of said queue monitoring subsystem, said reward computing subsystem, and said communication subsystem is automated.
The IBM claim requires at least one of the steps to be automated–as for example–embodied in a computer, whereas claim 1 of Bilski does not:
A method for managing the consumption risk costs of a commodity sold by a commodity provider at a fixed price comprising the steps of: (a) initiating a series of transactions between said commodity provider and consumers of said commodity wherein said consumers purchase said commodity at a fixed rate based upon historical averages, said fixed rate corresponding to a risk position of said consumer; (b) identifying market participants for said commodity having a counter-risk position to said consumers; and (c) initiating a series of transactions between said commodity provider and said market participants at a second fixed rate such that said series of market participant transactions balances the risk position of said series of consumer transactions.
Its not clear why Bilski did not add the requirement that a step be automated.
Google Seeks Patent on Chinese Spell Check Program
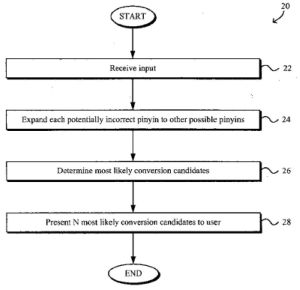 A patent application, published on January 31, shows Google is continuing to develop for the Chinese market. The application discloses a program for spell checking non-Roman character based languages, such as Chinese, Japanese, and Korean. Although the summary of the invention section provides that the program may cover any non-Roman based language, the dependent claims show the application is focused on the Chinese language.
A patent application, published on January 31, shows Google is continuing to develop for the Chinese market. The application discloses a program for spell checking non-Roman character based languages, such as Chinese, Japanese, and Korean. Although the summary of the invention section provides that the program may cover any non-Roman based language, the dependent claims show the application is focused on the Chinese language.
The program identifies potentially incorrect inputs, identifies alternatives, determines the proximity between the potentially incorrect input and the alternative, and computes probabilities of possible correct “word” based on the proximity measurement and optionally on a context of the possible conversion. Then it determines the most likely conversion from all the possible conversions.
——
“Fault-Tolerant Romanized Input Method for Non-Roman Characters,” Wu et. al. (U.S. Patent Application No. 20080028303).
IBM Patent Application: Customized Client-Side Search Indexing of the Web
 A recently published application shows IBM seeking a patent on a client-side search indexing program that works in conjunction with a server based search index to provide a users with personalized search results. Search result personalization is a long sought after goal. Google personalized search attempts to provided user customized results by retaining user data on the server-side. However, others have sought client side solutions. Jaime Teevan, et al.’s article “Personalizing Search via Automated Analysis of Interests and Activities” demonstrates that personalized client-side algorithms can significantly improve on current Web search results. Demand for improved search methods will increase with the ever expanding amounts of data.
A recently published application shows IBM seeking a patent on a client-side search indexing program that works in conjunction with a server based search index to provide a users with personalized search results. Search result personalization is a long sought after goal. Google personalized search attempts to provided user customized results by retaining user data on the server-side. However, others have sought client side solutions. Jaime Teevan, et al.’s article “Personalizing Search via Automated Analysis of Interests and Activities” demonstrates that personalized client-side algorithms can significantly improve on current Web search results. Demand for improved search methods will increase with the ever expanding amounts of data.
How to Admit or Exclude Prelimary Breathalyzer Results
 The February issue of the Illinois Bar Journal carries my article on “How to Admit or Exclude PBT Results” [Subscription Req.] [1]. PBTs are preliminary breath tests that are typically administered by the police on the scene of a traffic stop. The police use the results of a PBT as a factor to help establish probable cause to arrest a driver for driving under the influence of alcohol. PBTs are different and less reliable than the breath tests typically given at the police station—a.k.a. chemical tests—and therefore PBT results are treated differently than chemical test results. The article explains (1) when PBT results are admissible in court, (2) when the State is required to lay a foundation for their admission, and (3) what constitutes an adequate foundation.
The February issue of the Illinois Bar Journal carries my article on “How to Admit or Exclude PBT Results” [Subscription Req.] [1]. PBTs are preliminary breath tests that are typically administered by the police on the scene of a traffic stop. The police use the results of a PBT as a factor to help establish probable cause to arrest a driver for driving under the influence of alcohol. PBTs are different and less reliable than the breath tests typically given at the police station—a.k.a. chemical tests—and therefore PBT results are treated differently than chemical test results. The article explains (1) when PBT results are admissible in court, (2) when the State is required to lay a foundation for their admission, and (3) what constitutes an adequate foundation.
This article arose out of my work as a staff attorney at the Eighteenth Judicial Circuit Court of Illinois. However, the views express in the article are mine and not necessarily those of the Eighteenth Circuit.
———
[1] Eric R. Waltmire, How to Admit or Exclude PBT Results, 96 Ill.B.J. 92 (2008).
3D Printing and the Future of Innovation
Guy Kawasaki pointed me to this video of Chris Anderson talking about the topic of his next book–"the emerging world of free." His discussion of 3D printing technology got me thinking about how it might create a new class of inventors and innovation.
3D Printing in the World of Free. At 14:57 in the video, Chris states that 3D printing technology is introducing aspects of free into the world of physical products. He says 3D printing makes complexity free. Traditionally every bit of complexity in an item added more cost. However, every additional level of detail and complexity–i.e. grove in the surface–in a 3D printed item is free. The additional complexity cost nothing; the 3D printer head just takes a different path to make the detail required.
Chris says this ability to make physical complexity for free will dawn an "erra of impossibly detailed and fantastically complex products, which never would have made sense in the traditional manufacturing  environment, but are now happening because the cost is now zero." Chris also touched on 3D printing in his first book, The Long Tail (see page 225).
environment, but are now happening because the cost is now zero." Chris also touched on 3D printing in his first book, The Long Tail (see page 225).
Idea Lab is on the verge of releasing its Desktop Factory 3D Printer for $5000. At that price its targeted businesses and schools. A 5000 price seems a little steep for the mass market. But of course prices will come down.
3D Printing and Inventors. The Wall Street Journal has an article [no subscription required] discussing how companies are forming that use 3D printers to allow users to print 3D figures from online games. You create the figure and the company will print it and mail it to you. The article has this video that explains the state of the art of 3D printing. The video explains that the technology is not perfect, and the products created by a 3D printer may not be as refined and durable as desired. However, in the future it will be possible to create something of a computer or buy a product online, download instructions, and "print" the product right in your home. The video shows how a working flashlight can be printed using current technology. Certain 3D printers have the ability to print electronic components as well.
The pace of innovation and iterative invention will quicken when inventions or components of inventions can be quickly and cheaply printed and tested. So, will inventors purchase affordable 3D printers to prototype their inventions? I think so. As the price of 3D printers drop, the ability to easily create will increase the number of inventors and correspondingly the amount of innovation. Just as the web 2.0 has drawn many more to be participatory content creators, will 3D printers draw the masses to invention and create a new mass/class of inventors?
Suburban Networking: Silicon Prairie Social 2
 Today, the Silicon Prairie Social organizers announced their second technology networking event in the western Chicago suburbs. It’s happing on Thursday, January 24, 2008 from 6:30 pm to 10:00 pm at Mullen’s Bar & Grill in Lisle.
Today, the Silicon Prairie Social organizers announced their second technology networking event in the western Chicago suburbs. It’s happing on Thursday, January 24, 2008 from 6:30 pm to 10:00 pm at Mullen’s Bar & Grill in Lisle.
The purpose of the event is build mutually-beneficial business relationships between attendees. It is targeted at upwardly mobile tech professionals, tech executives, tech entrepreneurs, technology service providers, Internet professionals, Web 2.0 and startup companies, and the mobile industry.
RSVP here. See you there.